You are here
How do we train our people to face innovative and targeted cyber-attacks?
How do we encourage them to report security incidents? How do we make them feel responsible for cyber security?
Effective cyber security relies on people, processes and technologies. Your collaborators are your best line of defence and the pillars of your security. Their involvement in your cyber security plan and your involvement in business operations are key success factors of your security plan. This ideal situation requires more than making people aware of the risks, we need them to care, to take responsibility and to change their habits into safer ones.
As Bruce Schneier famously said: “Security is a process, not a product". This is even more true about cyber security awareness. Beyond awareness, the goal is to change behaviours and state-of-mind to keep your organisation safe.
Let’s build an effective human defence for your organisation; one of the most challenging cyber security projects but necessary to have an effective and sustainable security plan.
Why now more than ever?
- Homeworkers are the ideal target: The environment has a direct impact on the workers’ vigilance and with remote working, distance impairs the reaction time and communication with the IT.
- Cyber security is increasingly becoming a team effort. Having everyone involved, from IT to the business, is paramount to reach the level of protection you need. Fostering collaboration takes time and with increased attacks, you can’t afford to put it off any longer.
- Phishing is one of the easiest and fastest cyber-attacks with the biggest impact. Untrained organisations have a 40% chance of falling prey to phishing attacks – even if they are using the right technologies.
Your benefits
- Quickly reduce the chances of human error impacting your business by increasing the security knowledge of your teams.
- Fast deployment of a tailored security awareness program
- Efficient adoption and engagement of your teams
- Robust cyber security culture embedded within your organisation
- Best return on investment for your cyber security challenges
Our solutions
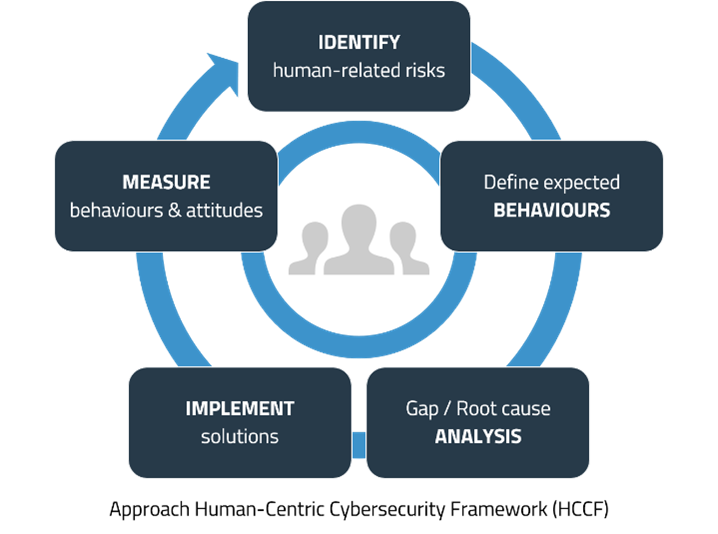 To achieve a cyber security awareness culture, we have developed a Human-centric cyber security framework – focusing on the most important factor: “Human attention is limited”.
To achieve a cyber security awareness culture, we have developed a Human-centric cyber security framework – focusing on the most important factor: “Human attention is limited”.
You therefore need to prioritise your actions and start with the most critical risks.
Our proven framework allows us to answer your cyber security needs and risks while promoting the best user experience.
We partner with leading security awareness platforms - such as KnowBe4 security awareness & training. Our objective: you get a faster and a more tailored use of the world’s largest and award-winning awareness contents for your organisation.
We are cyber security experts who speak your team’s tone of voice for early and efficient adoption. Our human-centric approach and our local support will help you engage your teams and get them ready regardless of their environment – key factors to successfully reduce the risks.
We take care of your cyber security awareness program on a long-term basis and provide valuable metrics to demonstrate short terms results and continuous improvements.
Why choose us?
- 20 years of cyber security and data privacy expertise
- Team of psychologists to understand the behavioural and cultural changes necessary to strengthen your cyber resilience
- Leading academic research on cyber security psychology and contributing to expert groups
- Our methodology complies with the European Network and Information Security Agency’s (ENISA) recommendations for a behaviour change framework
- Comprehensive & holistic approach considering people, processes and technologies for long term impact
- Local support to tailor the security awareness program to your needs and company culture for best return on investment
- Best affordable tools available in the market